Threat actors continuously refine their methodologies to bypass organizational defenses. Staying informed through reliable cybersecurity updates is critical for security professionals tasked with protecting sensitive data. The traditional paradigm of spra...
Read More
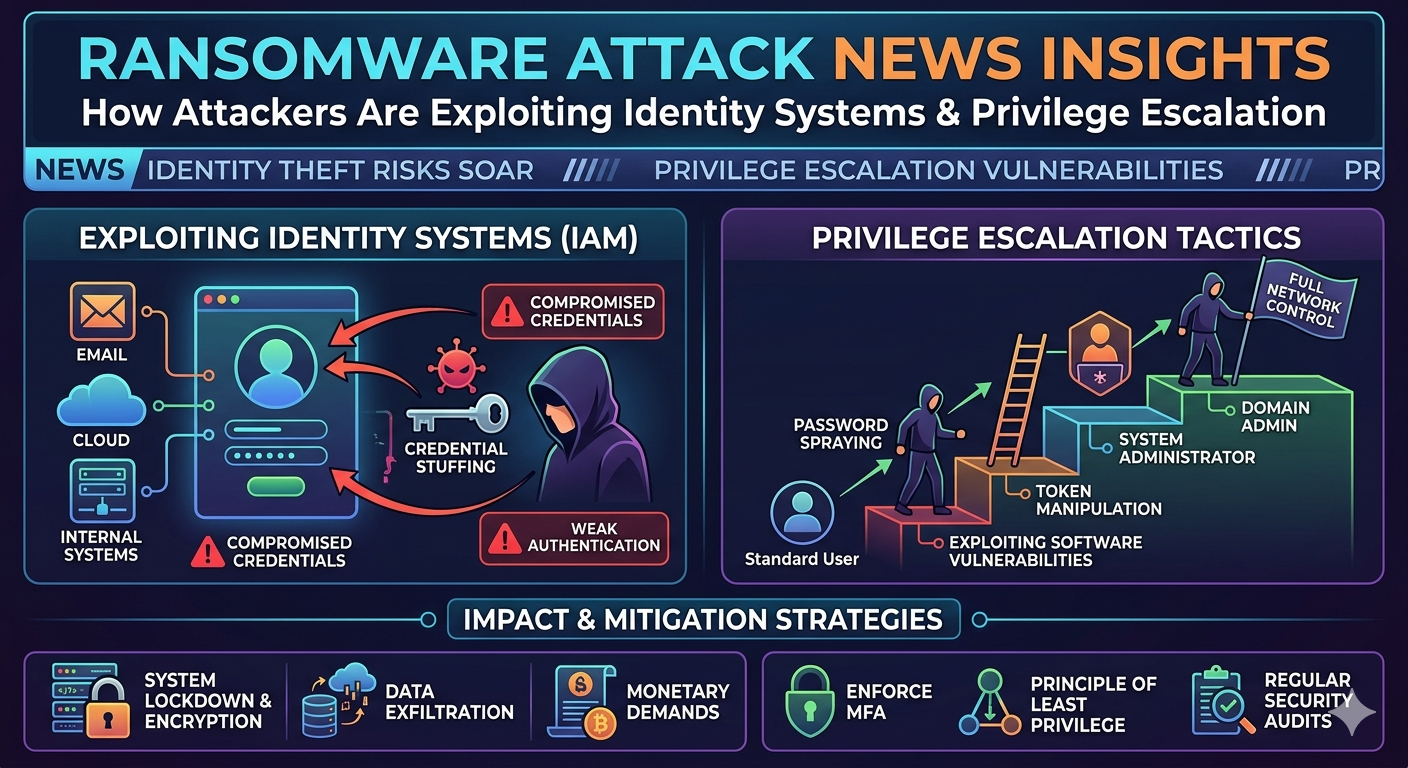
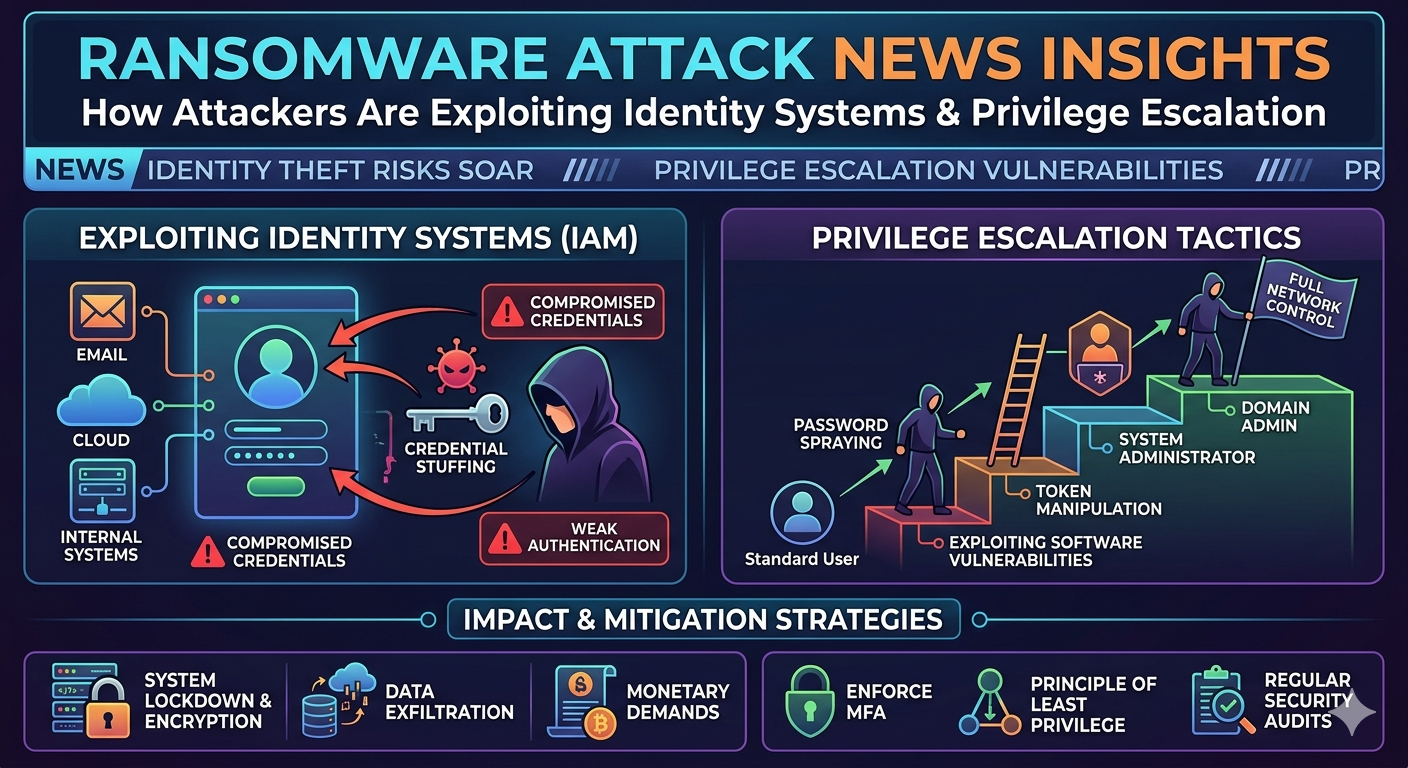
Recent security breach news highlights a troubling evolution in cybercriminal methodologies. Instead of relying solely on brute-force network penetration or complex malware payloads, threat actors are increasingly weaponizing identity management systems. ...
Read More

Internal communication platforms form the digital nervous system of modern organizations. Tools like Microsoft Teams, Slack, and Zoom facilitate rapid information exchange, integrating deeply with corporate directories and cloud storage repositories. Beca...
Read More

Monitoring daily hacking news reveals a distinct pattern in the modern threat landscape. Threat actors are rapidly discarding traditional, mass-distribution spam in favor of highly targeted, automated campaigns. At the core of this operational shift is ar...
Read More

Scanning the latest daily hacking news reveals a concerning shift in cybercriminal targeting strategies. Threat actors are increasingly moving away from standard corporate espionage and focusing their efforts on critical infrastructure. Facilities that co...
Read More
Recent ransomware attack news frequently highlights a troubling shift in adversary tactics. Threat actors no longer stop at encrypting primary data volumes. Instead, they actively seek out and compromise enterprise backup infrastructure before deploying t...
Read More

Security teams operate in an environment defined by continuous adversarial activity. New common vulnerabilities and exposures (CVEs) are published daily, creating a massive influx of data that security operations centers (SOCs) must process. Without a rel...
Read More

Enterprise networks face a growing threat as cybercriminals intensify attacks on edge routers and firewalls through sophisticated IoT botnet campaigns. These attacks exploit known vulnerabilities in devices that organizations often overlook during routine...
Read More

Enterprise VPN and remote access systems have become prime targets for sophisticated cyberattacks. Recent vulnerability news shows a troubling pattern: zero-day exploits targeting these critical security tools are on the rise, and 2026 is shaping up to be...
Read More

In the constantly evolving landscape of cybersecurity, tools come and go with the changing tides of technology. Yet, some names remain etched in the history books of ethical hacking. One such name is Cain & Abel. For many seasoned security professionals, ...
Read More

Cybersecurity professionals operate in an environment where seconds matter. A single exploited vulnerability can escalate from a minor breach to a catastrophic ransomware event in hours, or even minutes. Traditional methods of managing cyber risk—relying ...
Read More

For decades, the dominant strategy for cybersecurity was simple: build a wall. The castle-and-moat approach, or perimeter-based security, assumed that if you could keep the bad guys out, everything inside was safe. Firewalls, VPNs, and intrusion detection...
Read More

For years, the nightmare scenario for IT directors was simple: you come into the office, and everything is locked. Your files are encrypted, your operations grind to a halt, and a digital ransom note demands Bitcoin in exchange for a decryption key. While...
Read More

Ransomware attacks no longer begin with loud, destructive actions. Instead, today’s threat actors rely on patience, stealth, and precision. A growing pattern observed in ransomware news and daily hacking news reveals that most large-scale ransomware incid...
Read More

The threat landscape moves fast. Yesterday's patched vulnerability is today's zero-day exploit, and a tactic used against a small retail chain in the morning could be deployed against a multinational bank by lunch. For security professionals, keeping up f...
Read More

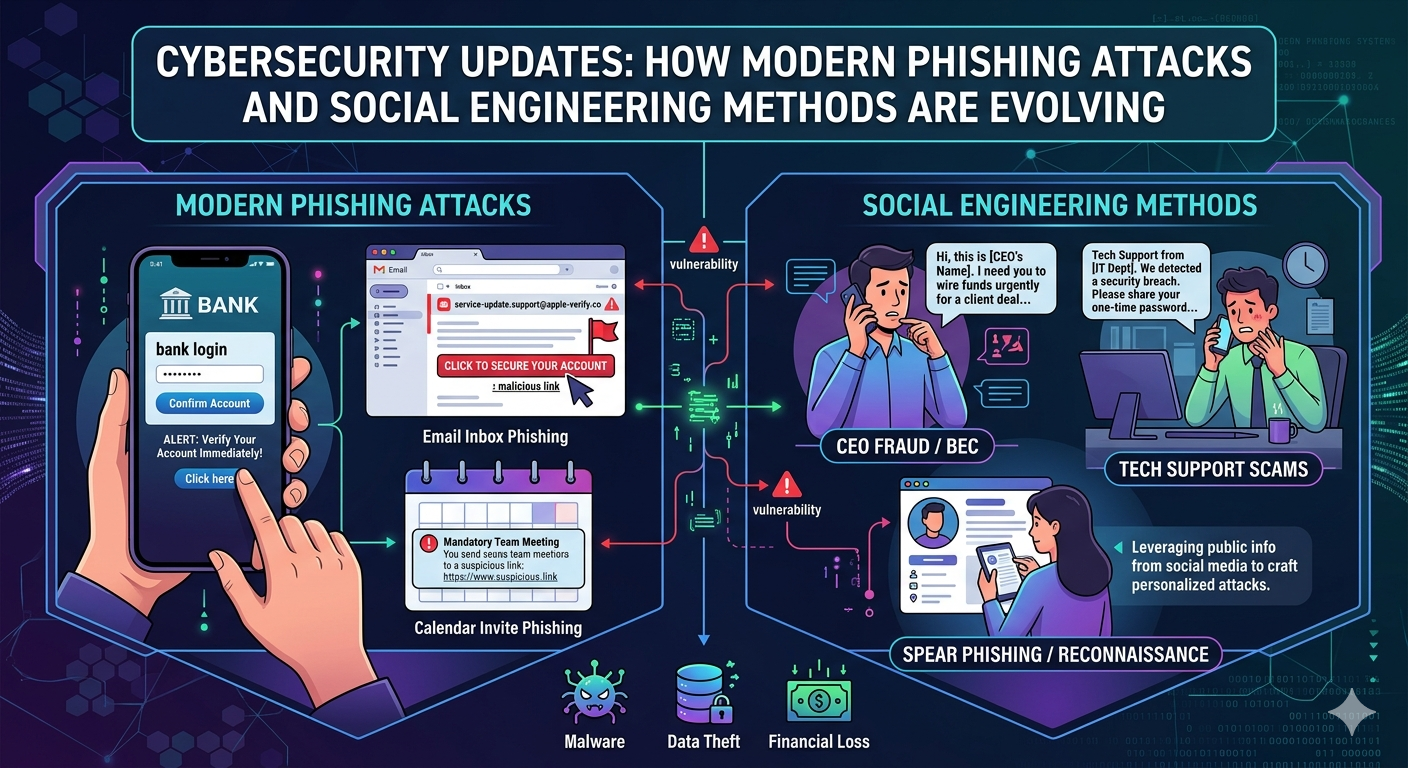
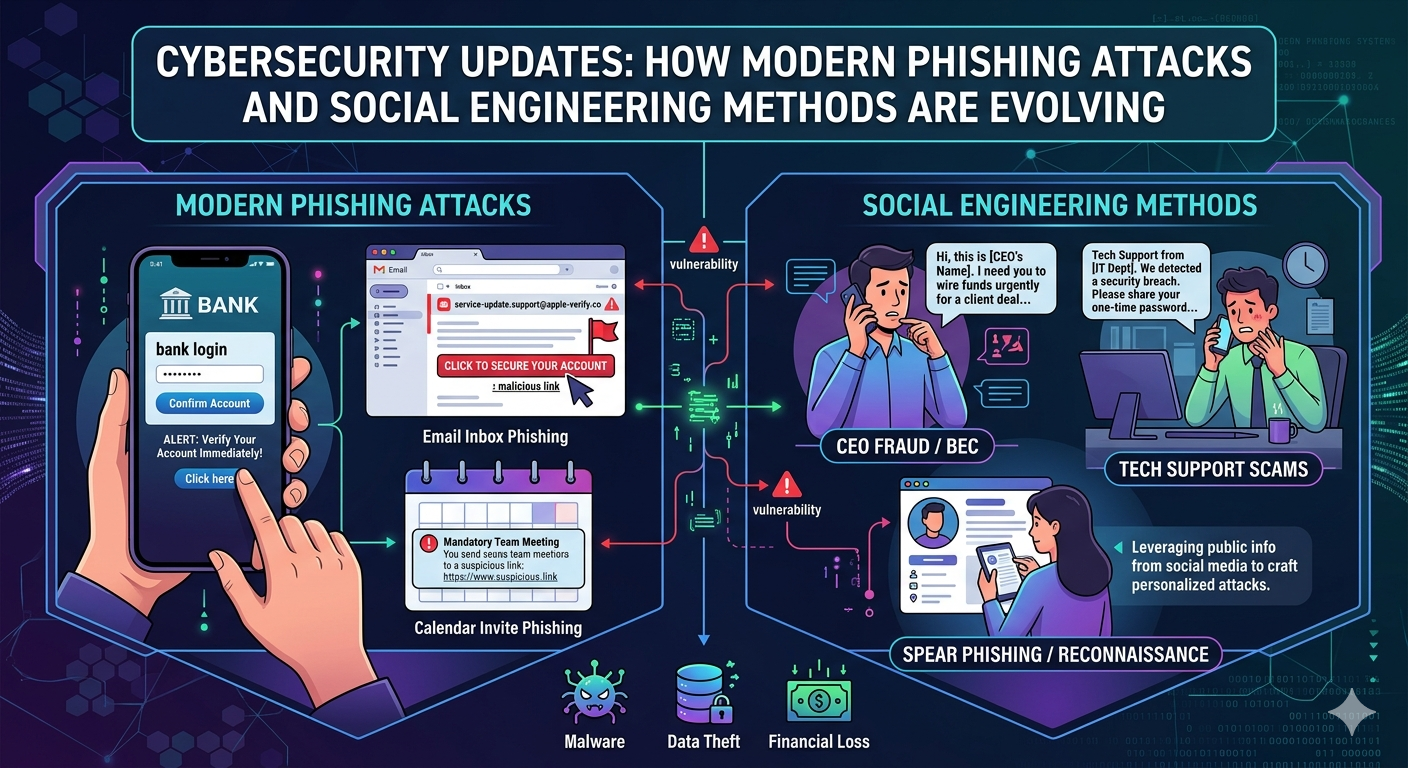
Most of us think we can spot a scam a mile away. We imagine poorly written emails from "princes" offering us millions of dollars or suspicious messages claiming we've won a lottery we never entered. But the reality of a modern phishing attack is far more ...
Read More

Smart devices are everywhere. From the watch on your wrist that tracks your steps to the home assistant that plays your favorite songs, these gadgets have seamlessly integrated into our lives. They offer convenience and connectivity, but they also open a ...
Read More

Cybercriminals have struck again, and this time the damage is staggering. A sophisticated phishing attack has compromised the personal data of millions of users across multiple platforms, leaving security experts scrambling to understand how such a widesp...
Read More

Ransomware has long relied on a critical vulnerability: human error. For years, cybercriminals have depended on someone clicking a malicious link, opening a compromised attachment, or falling for a phishing scam to gain access to a system. But a more soph...
Read More

Cyberattacks are becoming more frequent and sophisticated. For businesses, a single security breach can lead to devastating financial losses, reputational damage, and legal consequences. Staying informed about the latest threats isn't just a good practice...
Read More

When a ransomware breach makes the daily hacking news, the focus is almost always on a single, staggering number: the ransom amount. Whether it's millions demanded in cryptocurrency or a desperate negotiation playing out behind the scenes, this figure dom...
Read More

The line between legitimate online activity and malicious attacks is becoming increasingly blurred. Cybercriminals are constantly finding new ways to exploit trusted platforms to deceive unsuspecting users. A recent campaign by the Rhysida ransomware grou...
Read More

Cybersecurity threats continue to evolve at an alarming pace, with malware developers constantly finding new ways to infiltrate systems and exploit vulnerabilities. The latest addition to this growing arsenal is Atroposia malware, which has recently incor...
Read More

The Cybersecurity and Infrastructure Security Agency (CISA) has confirmed that malicious actors successfully exploited a Server-Side Request Forgery (SSRF) vulnerability in Oracle E-Business Suite, marking another significant cyberattack that highlights t...
Read More

For those who have been around the cybersecurity block a few times, the name Cain & Abel likely brings back memories. Developed by Massimiliano Montoro, this Windows-only tool was once a staple for password recovery and network sniffing. While its heyday ...
Read More

A newly discovered zero-day vulnerability, dubbed "RediShell," is actively being exploited in Redis servers, enabling attackers to achieve remote code execution (RCE) on exposed instances. This critical flaw allows malicious actors to take full control of...
Read More

Luxury department store Harrods has become the latest high-profile victim of a significant data breach, with hackers gaining access to personal information belonging to approximately 430,000 customers. This incident serves as another stark reminder that n...
Read More

Keeping up with the latest security news daily can feel overwhelming. New threats emerge constantly, and headlines about the latest ransomware attack news serve as a stark reminder of the risks businesses face. While a strong defense is crucial, what happ...
Read More

Cloudflare has confirmed it was the victim of a significant cyberattack over the Thanksgiving holiday. The attackers, believed to be a state-sponsored group, managed to access Cloudflare's internal Atlassian server, which included a Confluence wiki, a Jir...
Read More

Cyber threats are constantly evolving, making it harder than ever for businesses and individuals to protect their sensitive data. From sophisticated phishing schemes to advanced malware attacks, the digital world is filled with risks. Just keeping up with...
Read More

Artificial intelligence has fundamentally changed how we approach cybersecurity. What once seemed like science fiction—machines learning to detect threats in real-time—is now standard practice across organizations worldwide. But this technological evoluti...
Read More

Cybercriminals don't take holidays. As we advance deeper into the digital age, threat actors continuously evolve their tactics, exploiting new technologies and human vulnerabilities with alarming creativity. The cyberattack landscape of 2025 promises to b...
Read More

Cybersecurity professionals are scrambling to understand a sophisticated new threat actor that has emerged from the digital shadows. This previously unknown group has executed a series of coordinated attacks targeting financial institutions, healthcare or...
Read More

Ransomware attacks have become one of the most pressing threats in cybersecurity today. From hospitals unable to access patient records to entire city governments brought to a standstill, these attacks make headlines regularly for their devastating impact...
Read More

Cybercriminals are getting smarter. What started as obvious spam emails with broken English and suspicious links has transformed into sophisticated operations that can fool even tech-savvy professionals. Recent daily hacking news reports show that phishin...
Read More

The digital landscape has transformed dramatically over the past few years, bringing unprecedented opportunities alongside equally unprecedented risks. Cybersecurity today faces challenges that would have seemed like science fiction just a decade ago. Fro...
Read More

Cybersecurity professionals face an escalating battle against sophisticated threat actors who continue to refine their attack methods and target critical infrastructure. Recent cyber attack news reveals alarming trends in ransomware deployment, nation-sta...
Read More

Modern phishing attacks demonstrate a sophisticated understanding of human psychology and current events. Attackers quickly adapt their campaigns to exploit breaking news, natural disasters, or health crises to create urgency and emotional responses that ...
Read More
In today’s rapidly evolving digital landscape, cybersecurity has become a critical concern for individuals, businesses, and governments worldwide. As technology advances, so do the tactics of cybercriminals. A comprehensive cyber security review reveals t...
Read More

Phishing attacks have evolved from simple email scams to sophisticated operations that rival traditional businesses in their complexity. These aren't the obvious "Nigerian prince" emails of yesterday—modern phishing campaigns use psychological manipulatio...
Read More

Cybersecurity threats evolve at lightning speed. What seemed secure yesterday could be compromised today. For businesses, IT professionals, and security-conscious individuals, staying informed about the latest hacking incidents isn't just helpful—it's ess...
Read More
IntroductionIn today's digital age, cybersecurity has never been more critical. With the increasing frequency of major hacking incidents, IT professionals are facing an unprecedented challenge in protecting sensitive data and maintaining the integrity of ...
Read More

The digital frontier is evolving faster than many of us can keep up with, and cybersecurity stands at the center of it all. From AI-driven innovations to increasingly sophisticated ransomware breaches, 2025 serves as a pivotal moment to pause, reflect, an...
Read More

With the rise of data breaches and sophisticated phishing campaigns, staying informed about cybersecurity threats has never been more crucial. Cyber threats are evolving at an alarming rate, making it imperative for individuals and businesses alike to sta...
Read More

Phishing attacks have always posed a significant threat to cybersecurity, but the stakes are now higher than ever. With artificial intelligence (AI) becoming more sophisticated, attackers have upped their game, creating highly targeted, convincing, and di...
Read More

Staying informed about security threats is no longer optional—for professionals in today’s digital landscape, it’s a necessity. The rapid evolution of cyber threats like ransomware attacks and data breaches is reshaping how businesses defend themselves da...
Read More

Cyber attackers are getting smarter. Whether you run a business, manage IT, or simply use the internet every day, staying informed about emerging trends in cybersecurity today is critical for your digital safety. Risks, from AI-driven threats to complex p...
Read More

Ransomware attacks have become one of the most significant threats facing individuals and businesses today. With cyber criminals constantly evolving their tactics, understanding the risks and best practices is essential. This post will provide a comprehen...
Read More

Ransomware threatens everyone—from small startups to major enterprises. With new attacks disrupting businesses every week, “ransomware breach” and “cyber security daily” have become top priorities for leaders everywhere. But what exactly are ransomware br...
Read More

The number of cyberattacks is climbing, and their effects are growing more disruptive—from personal data breaches to global ransomware threats. You’ve probably seen the headlines. Hackers are now using advanced tools and sneaky tactics that make tradition...
Read More

Cybersecurity is no longer just an IT department concern—it's a boardroom priority and a daily worry for millions. From increasingly sophisticated phishing attempts to large-scale ransomware attacks that grab global headlines, understanding how cyberattac...
Read More

Ransomware attacks are not a distant threat. They’re affecting individuals, corporations, and even government systems daily. Imagine losing access to all your files at the click of a seemingly innocent email or link. That’s how ransomware operates, and to...
Read More

Cybersecurity threats are evolving at an unprecedented pace, and staying informed is crucial for individuals and organizations alike. From complex phishing attacks to sophisticated ransomware tactics, hackers are constantly refining their strategies. That...
Read More

Phishing attacks are becoming increasingly sophisticated, targeting individuals and businesses alike with devastating precision. With recent phishing scams making headlines and ransomware news highlighting massive financial losses, protecting yourself aga...
Read More

Cybercrime is evolving at a breakneck pace, with hackers leveraging cutting-edge technology to exploit vulnerabilities. From high-profile ransomware attacks to the explosion of phishing scams, the need to stay informed has never been greater. This blog br...
Read More

The digital landscape can feel like a minefield, with new cyber threats emerging every day. From phishing attacks that target your inbox to ransomware schemes that shut down entire networks, staying informed isn’t just important—it’s essential. But with s...
Read More

Cyberattacks are increasingly sophisticated and show no sign of slowing. From headline-grabbing ransomware news to more subtle phishing schemes, businesses are under constant threat of having their digital assets compromised. The damage can be catastrophi...
Read More

In today's digital landscape, cyberattacks have become a growing concern for individuals, businesses, and governments. Cybercriminals constantly develop new ways to exploit vulnerabilities, steal sensitive information, and cause financial or reputational ...
Read More
In today's digital world, cyberattacks have become more frequent, sophisticated, and damaging. Individuals and businesses alike are at constant risk of cyber threats that can lead to financial losses, data breaches, and reputational damage. This is why cy...
Read More
In today’s digital age, staying informed about cybersecurity is no longer optional—it’s essential. With cyber threats evolving at an unprecedented pace, keeping up with daily cybersecurity news can help individuals and businesses stay one step ahead of at...
Read More

In the blink of an eye, phishing attacks have become one of the most significant cyber threats facing businesses today. With attackers getting more sophisticated by the day, it’s crucial for companies to stay ahead of the curve. This isn't just about avoi...
Read More

Cybersecurity is an ever-evolving field, with new threats and vulnerabilities emerging daily. Keeping up with the latest security news is crucial for individuals and organizations alike to stay ahead of potential cyberattacks. In this roundup, we’ll explo...
Read More

Cyberattacks are no longer a distant possibility—they're a daily threat impacting businesses and individuals around the globe. From data breaches exposing sensitive information to phishing attacks stealing financial credentials, no entity is immune.This b...
Read More

Phishing attacks are among the most prevalent threats in cybersecurity today, with attackers becoming increasingly sophisticated in their methods. From cleverly disguised emails to malicious URLs, these scams target individuals and businesses alike, compr...
Read More

Cybersecurity threats evolve daily, and staying informed has never been more critical. Recent hacking news highlights how malicious actors are increasingly sophisticated, targeting not only large enterprises but also small businesses, individual users, an...
Read More

Ransomware breaches are one of the most pervasive and damaging types of cybersecurity threats facing organizations today. These attacks have become more sophisticated, leveraging advanced techniques to disrupt operations, compromise sensitive data, and ex...
Read More

Cybersecurity is no longer a niche concern—it’s a critical pillar of modern business operations. From the rise in sophisticated ransomware attacks to vulnerabilities in cloud infrastructures, staying informed about the state of cybersecurity today is esse...
Read More

Phishing attacks are on the rise—again. According to recent phishing attack news, cybercriminals are becoming increasingly sophisticated, targeting businesses and individuals alike with deceptive tactics that result in significant financial and data losse...
Read More

Phishing attacks continue to evolve, leaving even the most security-conscious individuals and organizations at risk. With headlines featuring phishing attack news almost weekly, it's clear that these cybercriminals are becoming more sophisticated. But wha...
Read More
The rapid proliferation of digital technologies has streamlined everyday operations for businesses, governments, and individuals alike. However, with these advancements comes an escalating wave of sophisticated cyber threats. Cybersecurity today is more c...
Read More

Ransomware attacks are back with a vengeance. Over the past few months, a surge in highly sophisticated cyberattacks has rippled across industries, leaving businesses scrambling to safeguard critical data and infrastructure. With reports of attacks target...
Read More

A coordinated cyber attack has recently shaken the global supply chain network, sending ripples across multiple industries. Targeting key logistics providers, manufacturing plants, and retail giants, the attack exposed vulnerabilities in IT infrastructure...
Read More

Cybersecurity today is more crucial than ever. With businesses, governments, and individuals relying heavily on digital systems, the threats posed by cybercriminals have grown exponentially. Enter ethical hacking—a critical pillar of modern cyber defense....
Read More
In today's swiftly advancing digital landscape, staying ahead of cyber threats is crucial for maintaining robust cybersecurity. As technology evolves, so do the tactics employed by cybercriminals, making it imperative for IT professionals and organization...
Read More

Cybersecurity is an ongoing battle. It's a game of cat and mouse where defenders must anticipate every move attackers make. But to truly safeguard digital spaces, one must first step into the shoes of those on the other side—hackers. This post aims to unr...
Read More

In the dynamic world of cybersecurity, one adversary has continually evolved, adapting to the measures meant to stop it—ransomware. This formidable cyber threat has grown from a crude tool of extortion into a sophisticated weapon used by hackers to crippl...
Read More

In the modern digital age, the threat of phishing attacks looms larger than ever. With headlines screaming about the latest phishing attack news and ransomware attack news, it’s clear that cybercriminals are upping their game. But how does this wave of cy...
Read More

In our hyper-connected world, the digital landscape is continuously evolving, and with it, the nature of cyber threats. Every day, individuals and businesses face an invisible storm of cyber attacks that disrupt lives, steal sensitive data, and even threa...
Read More

Decoding the Hacker's PlaygroundIn today's interconnected world, the line between cybercriminals and their unsuspecting victims is thinner than ever before. The world of hackers is not just a clandestine gathering of tech-savvy individuals hiding behind s...
Read More

In today's digital age, ransomware attacks are more prevalent than ever. While Bitcoin once dominated the landscape as the go-to ransom currency, cybercriminals have diversified their payment methods, switching to alternative forms of ransom. This blog po...
Read More

In today's hyper-connected world, the threat of ransomware attacks looms larger than ever. These malicious cyber-attacks can cripple businesses, disrupt essential services, and cause significant financial losses. For anyone concerned about the safety of t...
Read More

In today’s hyper-connected world, staying safe online has never been more challenging. Ransomware attacks are evolving, becoming more sophisticated and harder to detect. This blog post will explore the rising threat of ransomware, how these cyber threats ...
Read More

IntroductionIn today's digital age, no organization is immune to the rising tide of cybercrime. One of the most insidious forms of cyberattacks, ransomware, has recently made headlines by targeting the London branch of China's Industrial and Commercial Ba...
Read More

AI-powered cyber threats are on the rise, and as technology advances, so do the tactics of cybercriminals. This blog post explores the escalating threat landscape shaped by AI, its impact on our lives, and how we can prepare for an AI-driven future.Introd...
Read More

In the rapidly shifting landscape of cyber threats, ransomware has emerged as one of the most formidable adversaries for organizations and individuals alike. With each passing year, cyber attackers refine their tactics, making it increasingly difficult to...
Read More

IntroductionIn an era where cyber threats are evolving at a breakneck pace, traditional encryption methods are struggling to keep up. This shift has ushered in an urgent need for more robust and impenetrable security solutions. Enter quantum encryption—a ...
Read More

In an online world constantly under attack, staying informed about the latest cybersecurity threats and trends is a must. Cybersecurity is not just a concern for large corporations; it impacts small businesses, individual users, and everyone in between. T...
Read More

In our increasingly digital world, safeguarding personal and business data from cyber threats has never been more crucial. Cybersecurity updates are vital for protecting your data and maintaining privacy. In this blog post, we’ll explore the latest trends...
Read More

The Growing Importance of CybersecurityIn today's digital age, cybersecurity has become paramount. With every device, transaction, and communication moving online, the need to protect our data is more critical than ever. Cyber attacks are no longer rare o...
Read More

In a shocking turn of events, a significant cyber attack targeted Croatia's Split Airport, crippling operations and wreaking havoc on the travel plans of countless passengers. As one of the country's busiest airports, Split typically serves as a vital hub...
Read More

IntroductionIn a world that increasingly relies on technology, cybersecurity has become a paramount concern. Recently, a massive cyber attack targeted critical infrastructure, shaking the very foundations of our digital fortresses. This blog post aims to ...
Read More

IntroductionRansomware attacks are no longer just a concern for tech companies or large corporations. Today, they pose a serious threat to businesses of all sizes. With each passing year, ransomware incidents are becoming more frequent and sophisticated. ...
Read More

In today's interconnected world, cyber criminals are becoming more sophisticated in their attempts to deceive individuals and organizations. Phishing attacks are one of the most prevalent and dangerous forms of cybercrime, posing significant threats to da...
Read More

Cybersecurity breaches are becoming more frequent and sophisticated. For IT professionals, staying informed about the latest incidents and tactics is crucial.Introduction to the Growing Threat of Cybersecurity BreachesIn today's digital landscape, cyber t...
Read More

Introduction to Ransomware Ransomware has become one of the most significant and destructive cyber threats in recent years. Unlike traditional malware, ransomware encrypts a victim's data, rendering it inaccessible until a ransom is paid to the attacker. ...
Read More

In today's digital age, cybersecurity is not just a technical requirement but a critical aspect of any organization’s daily operations. The threat landscape is constantly evolving, with cybercriminals becoming more sophisticated in their tactics. For cybe...
Read More

Introduction to Phishing and Its EvolutionPhishing has long been a favored strategy for cybercriminals, evolving significantly since its inception. Initially, phishing attacks were relatively rudimentary, involving generic emails with suspicious links. Ho...
Read More

In today’s rapidly evolving digital landscape, staying updated with the latest ethical hacking news is not just beneficial—it’s essential. For IT professionals and cybersecurity enthusiasts, understanding current developments and emerging trends can mean ...
Read More

In an increasingly interconnected world, the digital landscape is both a boon and a potential minefield. Cybercriminals are constantly devising new and sophisticated ways to exploit vulnerabilities within critical infrastructure, and the emergence of the ...
Read More

In the ever-evolving realm of cybersecurity threats, the emergence of the BlackByte 2.0 ransomware has sent shockwaves through the digital landscape. This malicious software, characterized by its incredible speed and aggressive approach, has demonstrated ...
Read More