Recent security breach news highlights a troubling evolution in cybercriminal methodologies. Instead of relying solely on brute-force network penetration or complex malware payloads, threat actors are increasingly weaponizing identity management systems. By compromising legitimate credentials, attackers bypass traditional perimeter defenses entirely.
When reviewing the latest ransomware attack news, a clear pattern emerges across multiple industries: attackers are logging in rather than hacking in. Identity infrastructure, particularly Active Directory and cloud-based authentication services, has become the primary target for initial access brokers. Once inside, these actors use built-in administrative tools to escalate privileges and move laterally across the network.
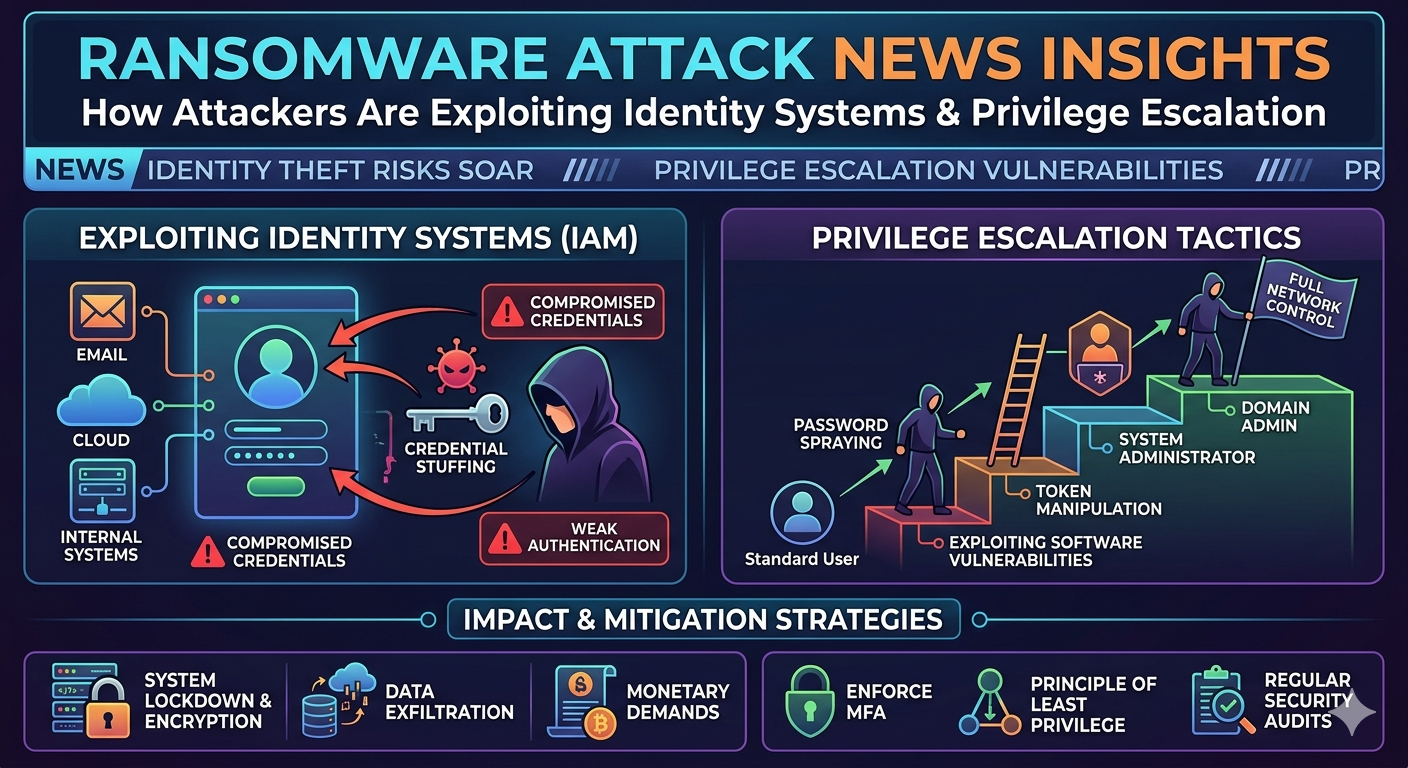
This post outlines how threat actors exploit identity systems and leverage privilege escalation to deploy ransomware. By understanding the mechanics behind the most recent security breach news, IT and security teams can implement structural defenses that neutralize these specific attack vectors and protect critical data assets.
The Shift in Ransomware Strategies
For years, ransomware operators relied heavily on malicious email attachments and drive-by downloads. While these methods still exist, the success rate of endpoint detection and response (EDR) solutions has forced attackers to adapt.
The most recent ransomware attack news indicates a pivot toward "living off the land" (LotL) techniques. By utilizing legitimate system tools like PowerShell and Windows Management Instrumentation (WMI), attackers evade detection. This approach requires valid user credentials, making identity systems the critical battleground for network security.
Moving Beyond Traditional Phishing
While phishing remains a prominent vector, threat actors now focus on acquiring session tokens and exploiting unpatched remote access gateways. Reports dominating security breach news often trace the root cause back to compromised VPN credentials or exposed Remote Desktop Protocol (RDP) instances. Once an attacker authenticates successfully, they blend in with normal administrative traffic, making detection exceptionally difficult.
How Attackers Exploit Identity Systems
Identity systems act as the central nervous system for organizational access. When these systems are compromised, the entire network is at risk.
Compromising Active Directory
Active Directory (AD) is a frequent target highlighted in ransomware attack news. Attackers often exploit misconfigurations within AD, such as weak service account passwords or excessive permissions granted to standard users. Techniques like Kerberoasting allow attackers to extract service account tickets and crack the passwords offline. Once a service account is compromised, the attacker gains a persistent foothold within the domain.
Abusing Multi-Factor Authentication (MFA)
Multi-factor authentication is a fundamental security control, but it is not immune to exploitation. Attackers have developed methods to bypass or manipulate MFA protocols. MFA fatigue, or prompt bombing, involves flooding a user's device with authentication requests until the frustrated user accidentally approves the login. Recent security breach news frequently cites this exact technique as the catalyst for major corporate compromises. Additionally, adversaries utilize adversary-in-the-middle (AitM) phishing frameworks to steal session cookies, bypassing the need for an MFA prompt entirely.
The Role of Privilege Escalation
Gaining initial access is only the first step. To deploy ransomware effectively across an enterprise, attackers must elevate their permissions. Privilege escalation involves transitioning from a standard user account to an administrator or system-level account.
Lateral Movement Techniques
Once an attacker secures a foothold, they map the network to locate high-value targets, such as domain controllers and backup servers. They use tools like BloodHound to visualize Active Directory relationships and identify the shortest path to Domain Admin privileges.
According to recent ransomware attack news, attackers frequently utilize Pass-the-Hash (PtH) techniques during this phase. By extracting password hashes from system memory using tools like Mimikatz, they authenticate to other machines on the network without ever needing the plaintext password. This lateral movement allows them to distribute the ransomware payload to thousands of endpoints simultaneously.
Defending Against Modern Threats
To counter these identity-centric attacks, organizations must adopt a zero-trust architecture. This model assumes that breaches will occur and requires strict verification for every access request, regardless of where it originates.
Implementing robust identity hygiene is critical. This includes regularly auditing Active Directory for misconfigurations, enforcing the principle of least privilege, and utilizing Phishing-Resistant MFA, such as FIDO2 security keys. Monitoring for anomalous login behavior and unusual lateral movement can provide early warnings before a full-scale encryption event occurs. Consistently analyzing security breach news helps security teams stay informed about emerging tactics and adjust their monitoring rules accordingly.
Securing Your Identity Infrastructure
The tactics dominating ransomware attack news prove that defending the network perimeter is no longer sufficient. Identity is the new perimeter. Threat actors will continue to target authentication mechanisms and exploit excessive privileges to execute their campaigns.
To protect your organization, prioritize the security of your identity management systems. Conduct regular vulnerability assessments of your Active Directory environments, implement strict conditional access policies, and train users to recognize advanced phishing and MFA fatigue attacks. By hardening your identity infrastructure, you can disrupt the attack chain and prevent your organization from becoming the subject of the next major security breach news headline.