Threat actors continuously refine their methodologies to bypass organizational defenses. Staying informed through reliable cybersecurity updates is critical for security professionals tasked with protecting sensitive data. The traditional paradigm of spray-and-pray email campaigns has largely been replaced by highly sophisticated, targeted operations. Threat groups now leverage advanced social engineering techniques, exploiting human psychology rather than strictly relying on software vulnerabilities.
Understanding the mechanics of a modern phishing attack is essential for developing robust security architectures. Attackers meticulously research their targets using open-source intelligence (OSINT) to craft highly convincing narratives. This evolution requires organizations to adapt their defensive postures, moving beyond basic email filters to comprehensive, multi-layered security frameworks. Examining the current threat landscape reveals specific trends in how these malicious campaigns are executed and sustained.
The Transition to Precision Targeting
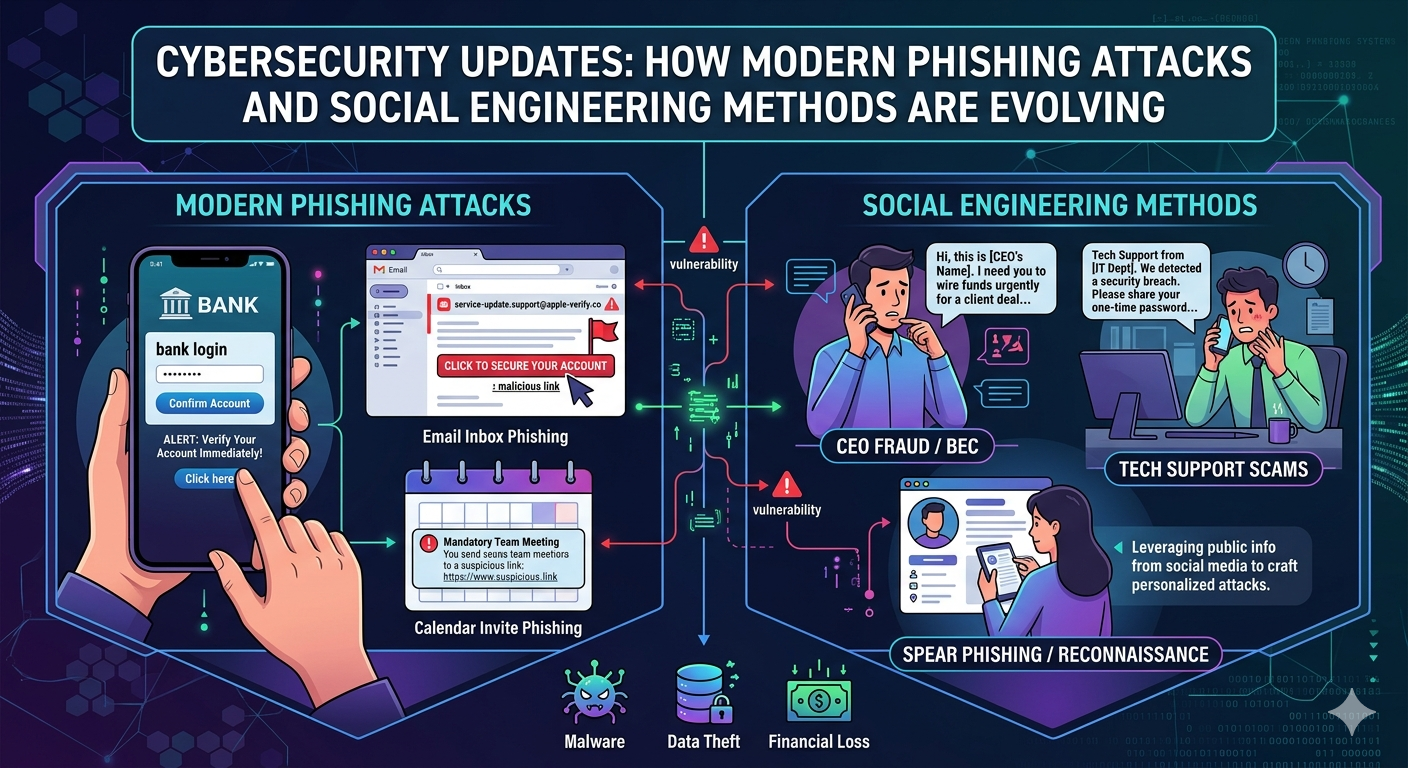
Early iterations of malicious email campaigns relied on volume. Attackers cast wide nets with generic messaging, hoping a small fraction of recipients would interact with the payload. Modern adversaries utilize a much more calculated approach. By gathering extensive background information from corporate directories, social media networks, and breached databases, attackers tailor their communications to specific individuals within an organization.
This level of personalization makes a targeted phishing attack highly effective. An employee in the finance department might receive an email appearing to come from the Chief Financial Officer, referencing an actual vendor the company utilizes. The email often contains urgent instructions to process a fraudulent wire transfer or a link to a credential-harvesting portal disguised as a legitimate corporate login page. Because the context aligns with the employee's daily responsibilities, the likelihood of compromise increases significantly.
Multi-Channel Social Engineering
The attack surface has expanded well beyond the corporate inbox. Security teams tracking recent cybersecurity updates note a sharp increase in cross-platform social engineering. Adversaries frequently initiate contact on one platform and move the target to another to establish credibility.
For instance, an attacker might send a SMS message (smishing) to a target's mobile device, posing as the IT department. The text warns of a synchronized password expiration and directs the user to a malicious domain. Alternatively, voice phishing (vishing) campaigns utilize spoofed phone numbers. The caller poses as a trusted entity, such as a bank representative or internal help desk technician, verbally coercing the victim into revealing multi-factor authentication (MFA) tokens or network credentials.
Artificial Intelligence in Threat Deployment
Artificial intelligence and machine learning have drastically altered the capabilities of threat actors. Generative AI tools allow attackers to draft flawless, highly persuasive copy, eliminating the grammatical errors and awkward phrasing that historically served as primary indicators of a phishing attack.
Furthermore, deepfake audio technology has been deployed in executive impersonation schemes. Attackers clone the voice of a high-ranking official and initiate a phone call to a subordinate, authorizing an immediate financial transaction. Automated reconnaissance scripts also enable threat groups to scan thousands of public profiles simultaneously, identifying high-value targets and generating customized attack vectors at an unprecedented scale.
Implementing Resilient Mitigation Strategies
Defending against these evolving methods requires a systematic approach. Organizations must prioritize continuous education, deploying simulated campaigns to test employee readiness. However, human awareness cannot serve as the sole line of defense.
Technical controls are paramount. Implementing robust email authentication protocols, such as DMARC, SPF, and DKIM, prevents domain spoofing. Deploying endpoint detection and response (EDR) solutions ensures that if a user executes a malicious payload, the system can isolate the affected machine before lateral movement occurs. Furthermore, transitioning to FIDO2-compliant hardware security keys provides a phishing-resistant layer of authentication, effectively neutralizing the impact of stolen passwords.
Frequently Asked Questions
What makes a modern phishing attack different from older methods?
Older methods relied on mass distribution of generic emails with obvious errors. A modern phishing attack utilizes detailed personal information, flawless language generated by AI, and multi-channel approaches to deceive specific targets.
How often should organizations review cybersecurity updates?
Security teams should monitor cybersecurity updates daily. Threat intelligence feeds, vendor patch notes, and alerts from organizations like CISA provide critical information regarding emerging social engineering tactics and newly discovered vulnerabilities.
Can artificial intelligence be used to stop these threats?
Yes. Defensive AI models analyze communication patterns, baseline user behavior, and scan inbound traffic for anomalies. When an email deviates from established norms, the system can quarantine the message before it reaches the inbox.
What is the most effective technical defense against social engineering?
While no single solution is foolproof, implementing phishing-resistant multi-factor authentication (such as physical security keys) offers the highest level of protection against credential theft resulting from social engineering.
Strengthening Your Defense Against Emerging Threats
The sophistication of social engineering tactics will continue to advance. Threat actors will inevitably find new ways to manipulate human behavior and bypass perimeter defenses. Maintaining a proactive security posture requires constant vigilance and a commitment to integrating the latest cybersecurity updates into your organizational strategy.
By understanding the mechanics of every potential phishing attack, security teams can implement strict access controls, deploy advanced behavioral analytics, and foster a culture of security awareness. Organizations must consistently evaluate their incident response plans and technical safeguards to ensure they remain resilient against the next generation of digital threats.